Business in Glossop - Managed IT Support
M
anaged IT Support Services for Businesses in Glossop: Comprehensive Solutions and Benefits
In today’s fast-paced digital landscape, businesses in Glossop are increasingly reliant on technology to drive their operations. Managed IT support services offer a strategic solution to ensure that these technological needs are met efficiently and effectively. This article delves into the various aspects of managed IT support, including its definition, core components, and the specific benefits it provides to small and medium enterprises (SMEs) in Glossop. As businesses face challenges such as cybersecurity threats and the need for “cloud solutions”, understanding managed IT support becomes crucial. We will explore how these services can enhance operational efficiency, improve security, and ultimately contribute to business growth. Key sections will cover network security solutions, cloud IT solutions, IT helpdesk services, and the costs associated with managed IT services.
What Are Managed IT Support Services and How Do They Benefit Glossop Businesses?
Managed IT support services encompass a range of IT solutions provided by third-party vendors to help businesses manage their technology needs. These services typically include network management, cybersecurity, data backup, and IT consultancy. By outsourcing these functions, businesses can focus on their core operations while ensuring that their IT infrastructure is robust and secure. The primary benefit of managed IT support is the ability to access expert knowledge and resources without the overhead costs of maintaining an in-house IT team.
Defining Managed IT Support and Its Core Components
Managed IT support involves several core components that work together to provide comprehensive IT solutions. These components include:
- Network Management: Ensuring that the network infrastructure is reliable and efficient.
- Cybersecurity: Implementing measures to protect against cyber threats and data breaches.
- Data Backup and Recovery: Regularly backing up data to prevent loss and ensuring quick recovery in case of incidents.
- IT Consultancy: Providing strategic advice on technology investments and improvements.
These components are essential for maintaining a secure and efficient IT environment, allowing businesses in Glossop to operate smoothly and effectively.
Key Advantages for Small and Medium Enterprises in Glossop
For small and medium enterprises in Glossop, the advantages of managed IT support are significant. These include:
- Cost Savings: By outsourcing IT support, businesses can reduce the costs associated with hiring and training in-house staff.
- Increased Efficiency: Managed IT services streamline operations, allowing businesses to focus on their core activities.
- Access to Expertise: SMEs gain access to a team of IT professionals with specialized knowledge and experience.
These benefits collectively enhance the operational capabilities of businesses, enabling them to compete more effectively in the market.
Which Network Security Solutions Protect Derbyshire Businesses Effectively?
Network security is a critical concern for businesses in Derbyshire, as cyber threats continue to evolve. Effective “network security” solutions are essential for safeguarding sensitive data and maintaining business continuity.
Essential Cybersecurity Measures for Local IT Support
To protect against cyber threats, businesses should implement several essential cybersecurity measures, including:
- Firewalls: These act as barriers between trusted internal networks and untrusted external networks, preventing unauthorized access.
- Antivirus Software: Regularly updated antivirus programs help detect and eliminate malware before it can cause damage.
- Regular Updates: Keeping software and systems updated ensures that vulnerabilities are patched promptly.
Implementing these measures significantly reduces the risk of cyberattacks and enhances overall security.
The importance of robust cybersecurity measures is underscored by the significant financial and operational risks that cyberattacks pose to businesses, particularly SMEs.
Cyberattack Risks and Prevention for SMEs
AbstractOver the past decade, the number of cyberattacks affecting United States small- and medium-sized enterprises (SMEs) has increased substantially; with an average per-breach loss of $500,000 USD. Cyber-breaches most often result in business closure within 6 months of the breach. A modified Delphi technique used with a 20-member panel of cybersecurity experts was conducted to discover ways SMEs could prevent these breaches.
Strategic cybersecurity risk management practices for information in small and medium enterprises, M Preiksaitis, 2022
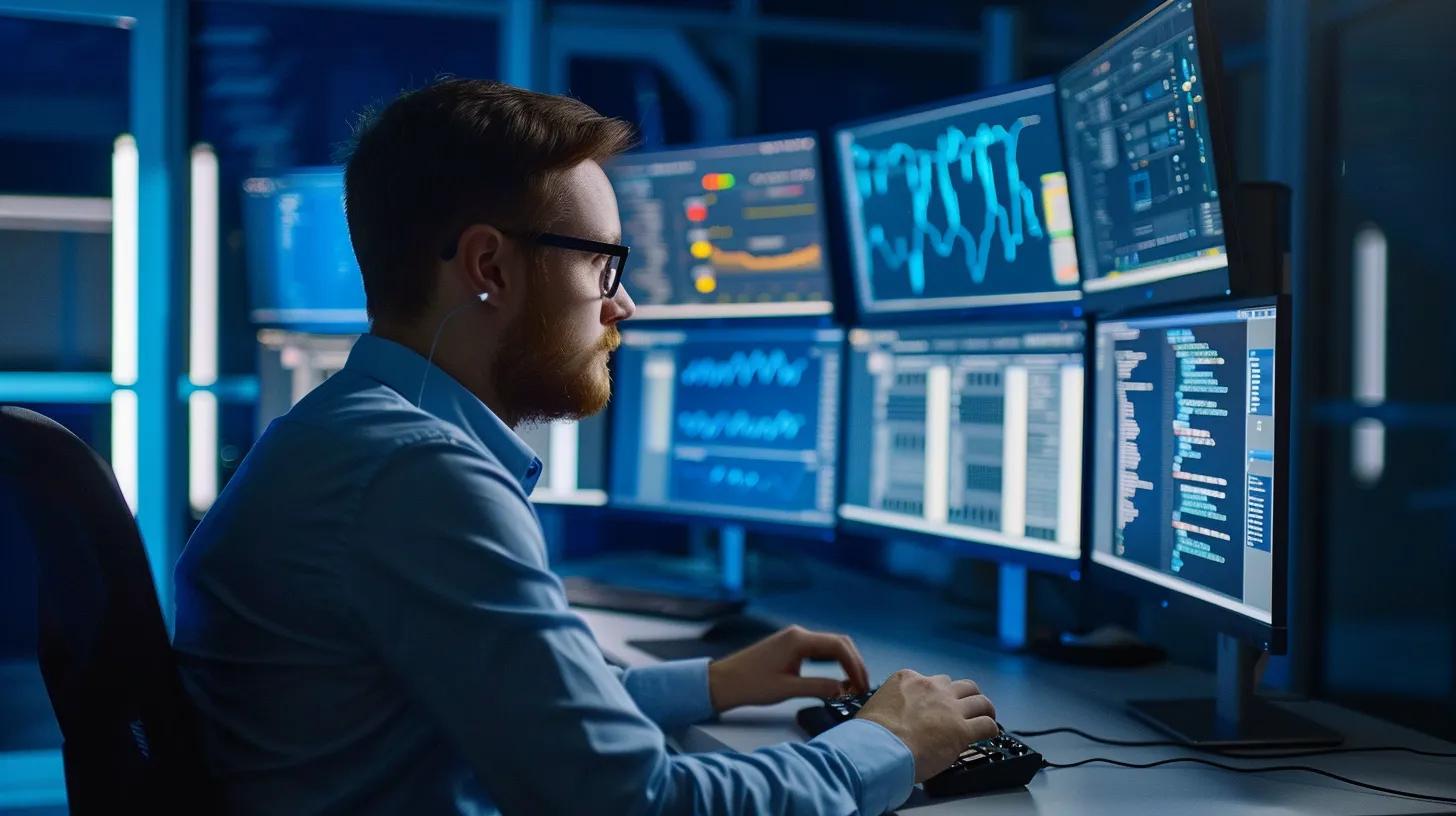
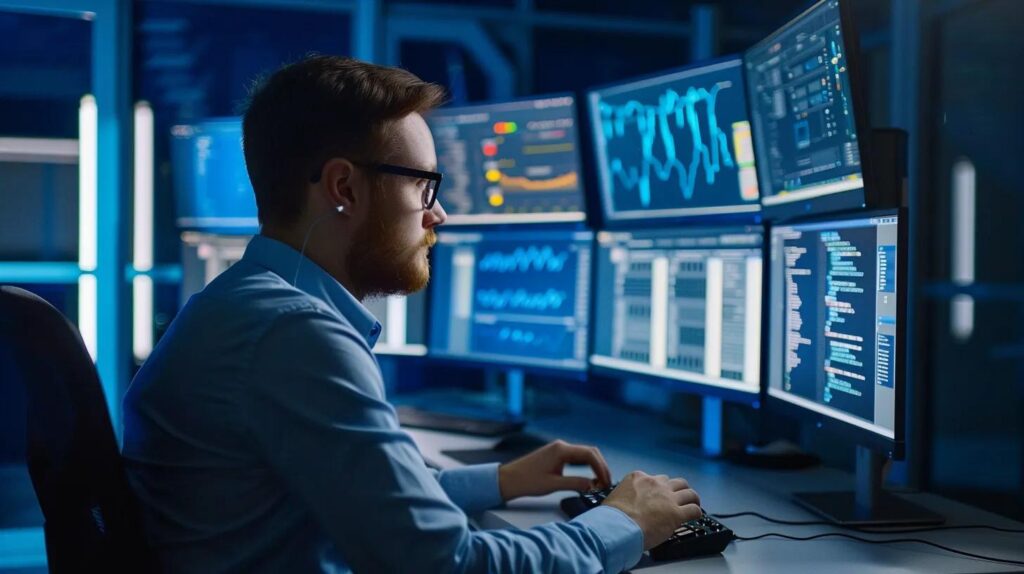
How Network Monitoring Enhances Business Security in Glossop
Network monitoring plays a vital role in enhancing business security by providing real-time insights into network activity. This proactive approach allows businesses to:
- Detect Threats Early: Identifying unusual activity can help prevent potential breaches before they escalate.
- Implement Proactive Response Strategies: Quick responses to detected threats can mitigate damage and protect sensitive information.
By investing in network monitoring, businesses in Glossop can strengthen their security posture and safeguard their operations.
How Do Cloud IT Solutions Improve Business Operations in Glossop?
Cloud IT solutions have revolutionized the way businesses operate, offering flexibility and scalability that traditional IT infrastructures cannot match. These solutions enable businesses to access resources and applications over the internet, facilitating remote work and collaboration.
Overview of Cloud Computing Services Tailored for Local Businesses
Local businesses can benefit from various cloud computing services, including:
- Infrastructure as a Service (IaaS): Provides virtualized computing resources over the internet.
- Software as a Service (SaaS): Delivers software applications via the cloud, eliminating the need for local installations.
- Platform as a Service (PaaS): Offers a platform for developers to build, deploy, and manage applications without the complexity of infrastructure management.
These services are customizable to meet the specific needs of businesses in Glossop, enhancing operational efficiency.
Benefits of Cloud Migration and Remote Access Solutions
Migrating to cloud solutions offers several advantages, such as:
- Cost Efficiency: Reduces the need for physical hardware and maintenance costs.
- Flexibility and Scalability: Businesses can easily scale their IT resources up or down based on demand.
- Improved Collaboration: Remote access solutions enable teams to collaborate seamlessly, regardless of location.
These benefits make cloud IT solutions an attractive option for businesses looking to enhance their operational capabilities.
Indeed, the adoption of cloud computing has become a transformative force for small businesses, offering a multitude of advantages that redefine operational paradigms.
Cloud Computing Benefits for Small Businesses
One of the popular technologies in the industry today is cloud computing and the use of cloud computing in small businesses is now fashionable, it has a remarkable impact on them by bringing a new way of working, accessing their data and storing it. The results of this study shows that there are several benefits that cloud computing has to offer small businesses if cloud computing is adopted and that includes flexibility, cost reduction and automatic software/hardware upgrades etc.
Adaptation and effects of cloud computing on small businesses, D Karagozlu, 2021
What IT Helpdesk Services Are Available for Glossop Businesses?
IT helpdesk services are crucial for providing technical support and resolving IT issues promptly. These services ensure that businesses can maintain productivity and minimize downtime.
24/7 Technical Support and Issue Resolution
Having access to 24/7 technical support is essential for businesses that rely on technology. This service allows for:
- Immediate Assistance: Quick resolution of IT issues minimizes disruptions to business operations.
- Expert Guidance: IT professionals can provide solutions based on their expertise, ensuring effective problem-solving.
This level of support is particularly beneficial for businesses that operate outside of traditional hours or have remote employees.
Customized IT Support Contracts for Local SMEs
Customized IT support contracts allow businesses to tailor their IT services to meet specific needs. Benefits include:
- Flexibility in Contracts: Businesses can choose the level of support that aligns with their operational requirements.
- Meeting Specific Business Needs: Tailored contracts ensure that businesses receive the services they need without paying for unnecessary extras.
This customization enhances the value of IT support services for SMEs in Glossop.
How Does IT Consultancy Support Business Growth in Derbyshire?
IT consultancy plays a vital role in helping businesses grow by providing strategic insights and recommendations on technology investments.
Strategic IT Planning and Infrastructure Management
Effective IT consultancy involves strategic planning and infrastructure management, which can lead to:
- Optimized IT Investments: Businesses can make informed decisions about technology purchases and upgrades.
- Improved Infrastructure: A well-managed IT infrastructure supports business operations and enhances performance.
These strategic insights are essential for businesses looking to leverage technology for growth.
Disaster Recovery and Remote IT Support Services
Disaster recovery planning is a critical component of IT consultancy. It ensures that businesses can recover quickly from unexpected events, such as data breaches or natural disasters. Key aspects include:
- Importance of Disaster Recovery: Having a solid recovery plan minimizes downtime and data loss.
- Remote Support Capabilities: Remote IT support allows for quick responses to issues, regardless of location.
This proactive approach to IT management is essential for maintaining business continuity.
What Are the Costs and Value of Managed IT Services in Glossop and Derbyshire?
Understanding the costs associated with managed IT services is crucial for businesses considering these solutions. Managed IT services can provide significant value through enhanced efficiency and security.
Pricing Models for Managed IT Support Services
Managed IT support services typically offer various pricing models, including:
- Flat-rate Pricing: A fixed monthly fee covers all IT services, providing predictable budgeting.
- Pay-as-you-go Pricing: Businesses pay only for the services they use, offering flexibility.
These models allow businesses to choose the option that best fits their financial situation and operational needs.
Return on Investment and Long-Term Benefits for Local Businesses
Investing in managed IT services can yield substantial long-term benefits, such as:
- Long-term Cost Savings: Reduced downtime and improved efficiency lead to lower operational costs.
- Increased Productivity: Access to expert support and resources enhances employee productivity.
These factors contribute to a strong return on investment, making managed IT services a valuable consideration for businesses in Glossop.
| Service | Pricing Model | Value |
|---|---|---|
| Network Management | Flat-rate | Predictable costs, comprehensive coverage |
| Cybersecurity | Pay-as-you-go | Flexibility, tailored to specific needs |
| IT Consultancy | Flat-rate | Strategic insights, optimized investments |
This table illustrates the various pricing models available for managed IT services and their associated values, helping businesses make informed decisions.